When you launch your trusted VPN software and head out into the wilds of the Internet, you justifiably presume your privacy to be protected. Your VPN should be masking your IP address from the sites you visit, altering the location of your PC and using its own DNS server to look up the addresses of the sites you visit, so even your Internet Service Provider (ISP) won’t be able to track what you’re doing.
However, you shouldn’t take this shield for granted. Whichever VPN service you use, whether free or paid, it’s worth performing some tests we recommend in this post to ensure that your VPN is doing its job correctly. You may compare the VPNs here!
It’s best to test your VPN in a location you assume to be safe, such as on your home network. First, you need to check for three main privacy threats – IP address, WebRTC detection, and DNS addresses. With your VPN switched off, go to ipleak.net. At the top, you’ll see your IP address, which is the unique number that identifies your connection to the Internet. Note down this IP address as you are going to need this for comparison purpose later on.
Below that is the WebRTC detection, which shows your IP address on the local network. This is a controversial service that deliberately leaks information about a PC’s connection to the Internet so that another PC can communicate with it directly, such as when making a video call.
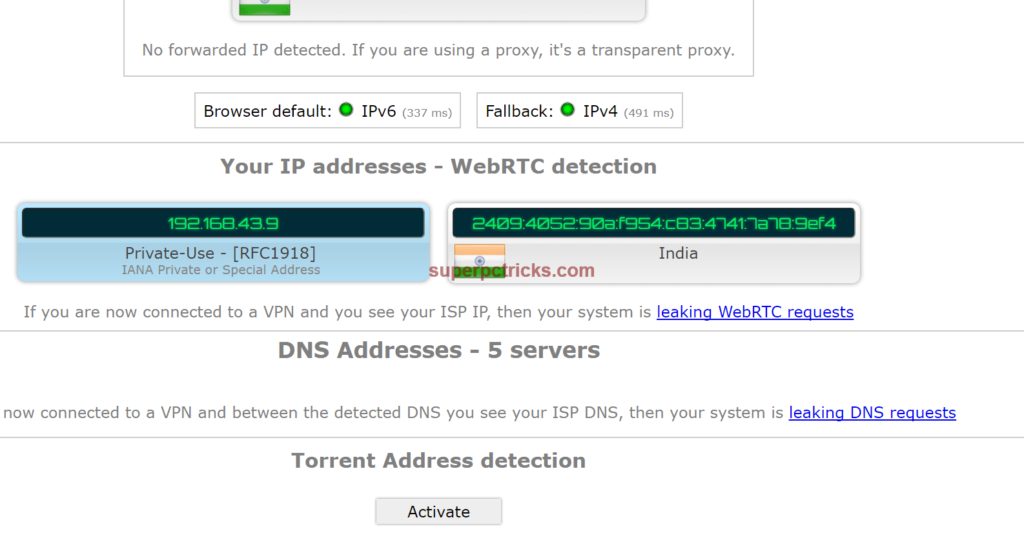 Further down is the DNS address. Your ISP manages this unless you’ve changed it to something else, but whoever controls it can see what sites you’re visiting. Unless the DNS owner states explicitly that it doesn’t keep a record of this data, you should consider that it keeps a record of every site you visit.
Further down is the DNS address. Your ISP manages this unless you’ve changed it to something else, but whoever controls it can see what sites you’re visiting. Unless the DNS owner states explicitly that it doesn’t keep a record of this data, you should consider that it keeps a record of every site you visit.
Now, its time to take privacy leak test of your VPN. Switch on your VPN and load the site again. You should see a set of different numbers. The first thing to check is the IP address. It should be different to your actual IP address shown in the above step, and depending on the VPN location you choose, may also be giving you the appearance of being in another country. This comes handy if you’re using your VPN to access geo-blocked sites and watch videos that are unavailable in your country.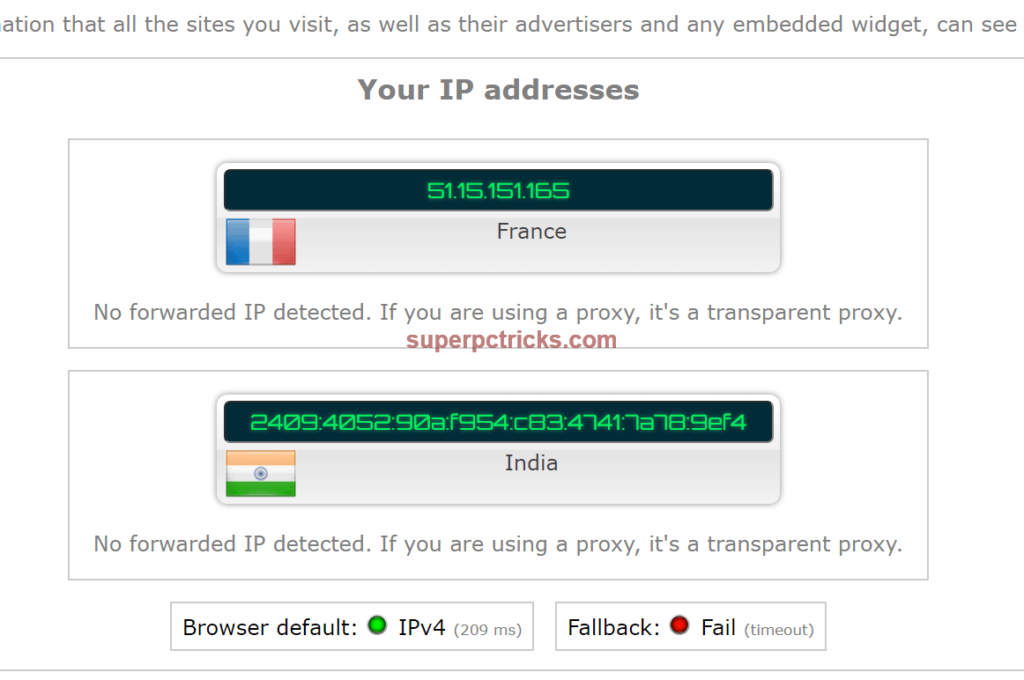 The WebRTC detection isn’t strictly controlled by your VPN, though some will block it. Here, your internal IP address should be displayed but within a Private Use box, with no reference to your ISP. If your ISP’s name appears here, there’s a good chance that your privacy is being jeopardized.
The WebRTC detection isn’t strictly controlled by your VPN, though some will block it. Here, your internal IP address should be displayed but within a Private Use box, with no reference to your ISP. If your ISP’s name appears here, there’s a good chance that your privacy is being jeopardized.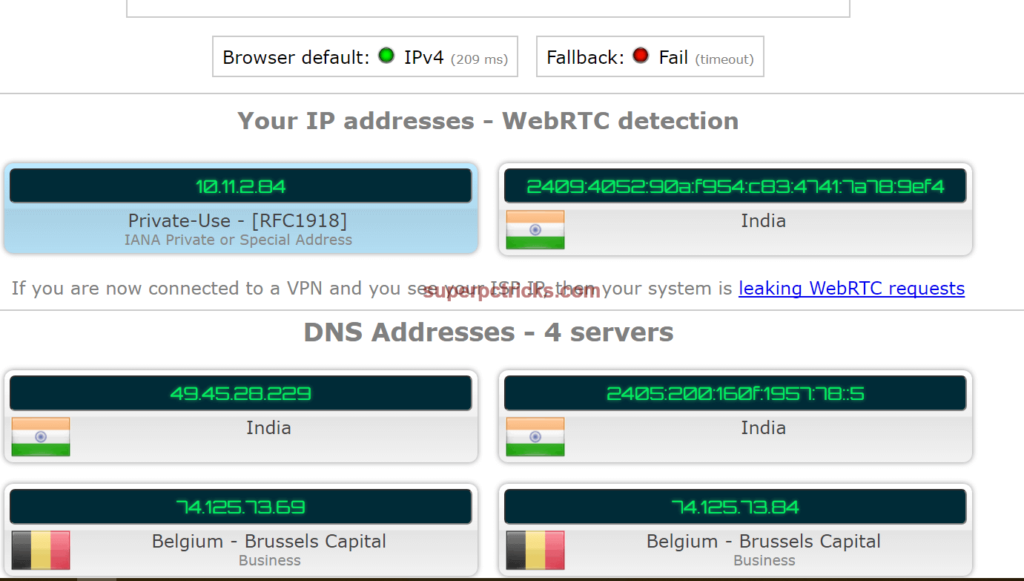 If you find that your WebRTC information is leaking, you need to change your VPN. Voidsec (voidsec.com), the organization that discovered and first highlighted the problem, has information about it here, where you’ll also find a link to a spreadsheet of all the VPNs they’ve tested. We recommend you to choose one with a green cell in the Leak/Vulnerable column.
If you find that your WebRTC information is leaking, you need to change your VPN. Voidsec (voidsec.com), the organization that discovered and first highlighted the problem, has information about it here, where you’ll also find a link to a spreadsheet of all the VPNs they’ve tested. We recommend you to choose one with a green cell in the Leak/Vulnerable column.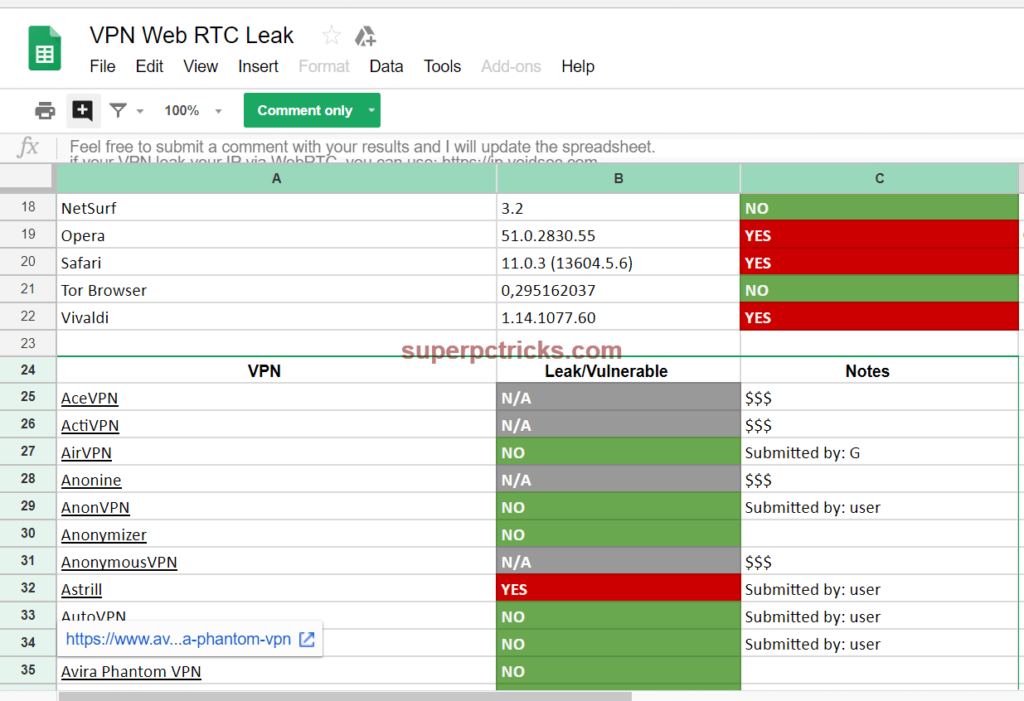 If you prefer, you can fix this security hole manually in your browser. In Chrome, you can download Chrome extension WebRTC Network Limiter offered by webrtc.org. In Firefox, enter about:config in the URL bar and double-click media.peerconnection enabled to set it to False. This might stop some video services operating, though. So if your specific video calling service stopped after this, undo the changes.
If you prefer, you can fix this security hole manually in your browser. In Chrome, you can download Chrome extension WebRTC Network Limiter offered by webrtc.org. In Firefox, enter about:config in the URL bar and double-click media.peerconnection enabled to set it to False. This might stop some video services operating, though. So if your specific video calling service stopped after this, undo the changes.
Back in ipleak.net, at the bottom, you’ll find the DNS address. This should make you seem as if you’re in the same country as your IP address. The DNS server address should also be changed from the one shown before switching on the VPN.
Below the DNS info is Torrent Address Detection. If you use BitTorrent software to share files, click Activate to see whether your VPN is allowing your torrent software to expose your IP address. Click the Activate button under Geolocation detection to check whether your browser asks permission before revealing your whereabouts.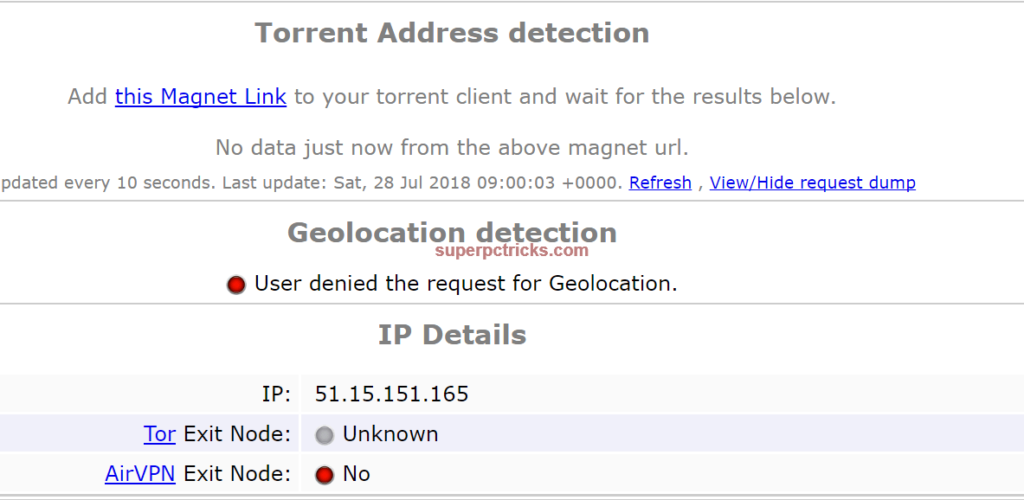 If you’re curious to know what further information is slipping out about you, your Internet activity and your PC, scroll down the page. You should see a map hopefully, showing your VPN’s location (not yours), as well as information about your computer hardware and browser.
If you’re curious to know what further information is slipping out about you, your Internet activity and your PC, scroll down the page. You should see a map hopefully, showing your VPN’s location (not yours), as well as information about your computer hardware and browser.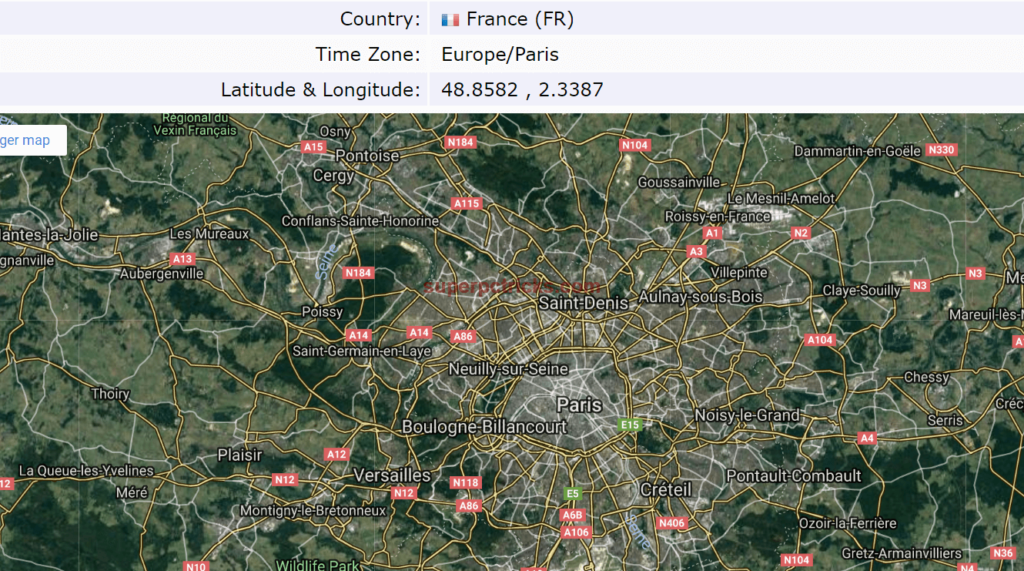
[…] handy Firefox browser plugin that lets you clean up your PC and take control of cookies, so you can avoid being traced online. You do not need to locate cookies manually to get rid of them. This Firefox extension does all for […]